The Internet Doesn’t Divide by Country. It Divides by 100,000 Numbers
Before getting to Netflix, you need to understand how internet routing actually works — because this is the thing VPN marketing carefully avoids explaining.
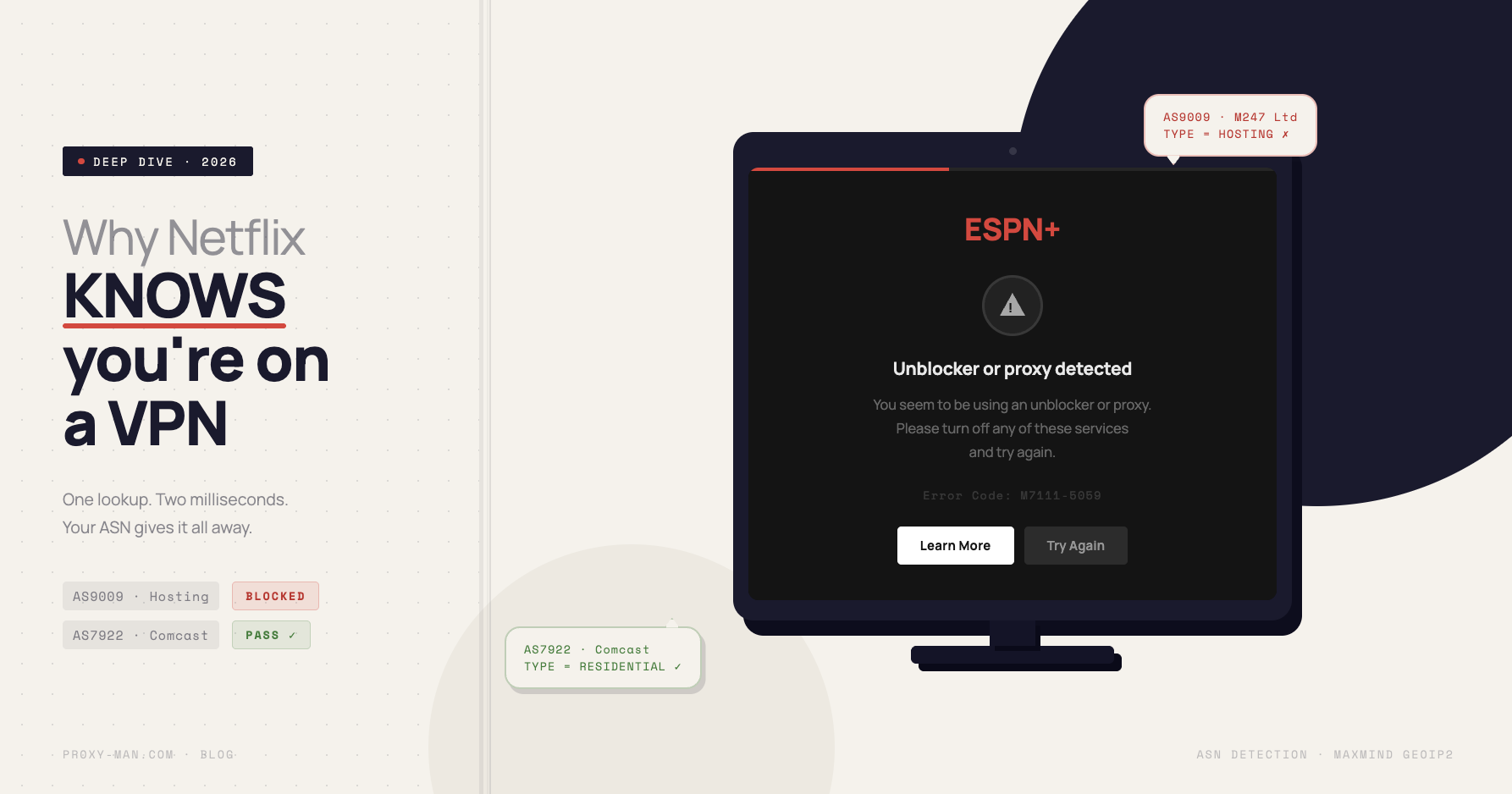
Every major network operator on the internet has a unique public identifier called an ASN — Autonomous System Number. These are not secrets. They are public, searchable, and tagged by type. AS7922 is Comcast. AS15169 is Google. AS16509 is Amazon Web Services. AS14061 is DigitalOcean. AS9009 is M247 — the hosting provider that powers a significant share of commercial VPN exit nodes.
When you browse the web through your home internet connection, your IP address belongs to your ISP’s ASN — Comcast, AT&T, Verizon, Deutsche Telekom. Databases like MaxMind GeoIP2, which Netflix, Hulu, banks, and anti-fraud systems all license, tag that ASN as residential. When you turn on a VPN, your IP address suddenly belongs to the ASN of whatever data center the VPN provider rented servers in. MaxMind tags that ASN as hosting. This classification is updated weekly and costs about 2 milliseconds to check.
The mental model that reframes everything: you thought the VPN was disguising you as an American. It was actually disguising you as a data center.
It’s like walking into a restaurant in Las Vegas wearing a t-shirt that says “Amazon AWS Employee, Ashburn, Virginia.” The server knows you’re not a local tourist — even if you speak with a perfect accent and paid for your seat.
According to the Hurricane Electric BGP Toolkit, roughly 115,000 active autonomous systems are registered in the public internet. Every one of them is publicly labeled as ISP, Hosting, Business, or Education — and any server in the world can read that label on the first request.
How Netflix Broke the Entire VPN Industry Overnight in 2016
In January 2016, Netflix announced global expansion into 130+ countries simultaneously. That same year, under pressure from Hollywood studios — Sony Pictures, Warner Bros., Disney — that had already sold territorial content licenses, Netflix launched a systematic VPN-detection system. What happened next was technically simple and commercially devastating for VPN providers.
Netflix began filtering all traffic by ASN type. If the IP belongs to an ASN classified as hosting — AWS, DigitalOcean, Hetzner, OVH, Linode, M247 — it’s treated as physically impossible for a real home user to have that IP. Block. This is not machine learning. It’s not neural networks. It’s not magic. It is one SQL join between the IP of the incoming request and a table of ASN types.
The reason this is a perfect and cheap defense: VPN providers cannot leave hosting ASNs. They rent servers from AWS, OVH, DigitalOcean. The moment a VPN company registers its own ASN, it gets tagged as hosting. The moment it buys an IP block from a data center, that block is already tagged. There is no architectural escape within the VPN model.
Since 2016, the same detection method has been copied by ESPN+, DAZN, BBC iPlayer, Hulu, Disney+, Amazon Prime Video, and Max. An academic study — An Empirical Analysis of the Commercial VPN Ecosystem (Khan et al., ACM IMC 2018) — found that 62 of the top 200 VPN providers host all their infrastructure across just five providers: AWS, OVH, DigitalOcean, Hetzner, and M247. Their ASNs are trivially identifiable in a single lookup.
Netflix’s press release framed this as protecting content partners. In practice, it meant that anyone using a commercial VPN to access a streaming service from abroad was now playing an arms race they structurally could not win.
The Scene: You Paid for ESPN+, You Can’t Watch UFC
Here’s the scene, reconstructed from what actually happens to hundreds of thousands of people every fight night.
It’s Sunday, 11:00 PM. The UFC title fight is live. You’re on the couch with a beer, laptop open. You paid $10 for the ESPN+ pay-per-view — legally, through the app, with your card. You’re in Berlin visiting family. The fight is blacked out in your current location due to regional broadcast rights. You launch NordVPN, pick a US East server, and hit Play.
“You seem to be using an unblocker or proxy.”
You switch to ExpressVPN. Same message. Surfshark — infinite loading spinner. One service throws Error M7111-5059. You try a server in Miami, Dallas, Chicago. Each one fails within seconds. By the time you’ve cycled through four VPN apps, the first round has ended. Your phone battery is at 18%.
This is the ESPN+ moment. Almost everyone who has used a VPN for streaming has their own version: the Netflix library that suddenly shows only regional content, the DAZN soccer match that won’t load, the BBC iPlayer documentary you can’t finish. A GlobalWebIndex survey found that roughly 31% of VPN users in Europe cite access to streaming content as their primary reason for subscribing — and in the same survey, 47% report being blocked by streaming services despite using a VPN.
This is the exact moment people first search “residential proxy.” Not because they read about it. Because they’ve exhausted every VPN on the market and realized they’ve been carrying a tool designed for a different problem.
Residential IP: How to Look Like a Couch, Not a Server Rack
A residential proxy is not a “better VPN.” It is a structurally different thing, and the difference maps exactly to the ASN problem described above.
A residential IP is an IP address that belongs to a consumer ISP’s ASN — Comcast, Verizon, AT&T, Deutsche Telekom. To MaxMind and to Netflix, this is literally indistinguishable from a regular home user — because it is a real IP address on a real home router. The ASN check, which instantly flags a VPN, returns “residential” for a residential proxy and moves on.
Residential proxy providers get access to these IPs through SDK agreements with mobile and desktop app developers, where users consent to share idle bandwidth in exchange for a free app or service. This is where the ethical gradient matters — and it’s worth being direct about it: not all residential proxy providers source IPs the same way. Some operate transparent opt-in networks where users are clearly informed and compensated. Others bury consent in 40-page terms of service that no one reads. A 2019 USENIX Security study (Resident Evil: Understanding Residential IP Proxy as a Dark Service, Mi et al.) documented that a significant share of IPs in commercial residential pools came from apps whose users had no real awareness they were acting as exit nodes. Ask your provider where the IPs come from before you buy.
Mobile proxies go one level further. A 4G/LTE IP belongs to a mobile carrier’s ASN — AT&T Mobility, T-Mobile, Verizon Wireless. But what makes mobile ASNs almost impossible to block is CGNAT — Carrier-Grade NAT. Mobile operators share a single public IPv4 address among hundreds or thousands of real subscribers simultaneously. According to APNIC Labs, roughly 90% of mobile internet traffic worldwide passes through CGNAT. Blocking a mobile IP means blocking an entire neighborhood’s worth of real users. Instagram, TikTok, and streaming services simply cannot afford to aggressively filter mobile ASNs — the collateral damage is too large.
This is not about anonymity from governments or law enforcement. It’s about something narrower and more honest: being indistinguishable from a normal user to an automated classification system. That’s the problem residential and mobile IPs solve. That’s the problem VPNs, by architecture, cannot.
What the VPN Industry Won’t Tell You
VPN marketing is built on the phrase “protect your privacy.” Technically, a VPN protects you from two specific things: your ISP seeing your traffic, and snoopers on public Wi-Fi. That’s a real and valid use case. But here’s what the marketing doesn’t say: a VPN does not protect you from the service you’re connecting to. Any website that checks your ASN immediately sees that you are not a home user — you are a customer of VPN provider N, running through infrastructure in Romania or the Netherlands.
Beyond detection: VPN providers log. Despite “no-logs” marketing language, several providers have been caught doing exactly that. In 2017, PureVPN handed logs to the FBI that helped identify a user — despite their public zero-logs policy. The case was United States v. Ryan Lin, and the Department of Justice press release is public record. IPVanish and others have faced similar disclosures between 2021 and 2023.
Residential proxies are structurally different in this respect, though not for the reason VPN marketing would frame it. Because traffic routes through thousands of different real IPs rather than through a single provider’s exit node, there is no single point that holds a log of your sessions. This is not a privacy guarantee — it is a different architecture. The provider still knows your account; the exit node operator does not know who you are.
An academic review of 283 mobile VPN apps — An Analysis of the Privacy and Security Risks of Android VPN Permission-enabled Apps (Ikram et al., ACM IMC 2016) — found that 38% contained outright malicious behavior and 75% used third-party tracking within the app itself. The privacy tool was collecting the data it claimed to protect.
The clarifying frame: VPN solves the problem of the 2010s — encrypting the channel between you and the exit node. Residential proxy solves the problem of the 2020s — looking like a real user to the service at the other end. These are two different tools that the market has crammed into the same cabinet and sold with the same marketing language. They are not the same product.
When to Use a VPN, When Residential, When Mobile — an Honest Breakdown
This is not a ranking. It’s a matching exercise. The right tool depends entirely on what you’re trying to do.
- Use a VPN when
- You’re on public Wi-Fi and want to encrypt your connection from network snoopers. You need a secure tunnel to a corporate network. You want to prevent your ISP from seeing your browsing traffic. VPN is the right tool for channel security — it was designed for exactly this.
- Use a residential proxy when
- You want to watch streaming content from another country. You need to check geo-targeted prices on e-commerce or travel sites. You’re doing competitive intelligence on platforms that profile ASN origin. You’re managing multiple accounts on platforms that flag hosting IPs. The residential ASN is what passes the check that blocks VPNs.
- Use a mobile proxy when
- You’re working with Instagram, TikTok, or Meta Ads accounts at scale. You’re up against the hardest anti-fraud stacks — sneaker sites, betting platforms, anything that treats hosting and residential IPs with suspicion. The CGNAT reality of mobile carrier ASNs makes aggressive filtering practically impossible without unacceptable collateral bans on real users.
- Use a datacenter proxy when
- You’re running large-scale web scraping or search engine requests where speed matters more than ASN classification. The target site doesn’t apply anti-fraud logic, or you’re rotating at high volume where the cost of residential IPs would be prohibitive. Datacenter IPs are orders of magnitude cheaper and faster — they’re the right tool when detection isn’t a variable.
The key shift in thinking: this is not one product. It’s a toolkit. The problem with the VPN market is that it sold one product as the answer to all four problems, while only reliably solving the first. If you want all three IP classes accessible from one account — residential, mobile, and datacenter — that’s exactly how PROXY-MAN is structured: one dashboard, one balance, REST API and Telegram bot, pay by traffic or monthly. Worth knowing that option exists.